Michigan, US, 16th August 2024, ZEX PR WIRE, Guided Hacking is excited to announce the launch of its new Binary Exploit Development Course, aimed at breaking down the complex concepts behind binary exploitation and bringing this craft to a larger audience. This in-depth course is designed to take learners from foundational concepts to advanced techniques in exploit development, starting with the essential topic of buffer overflows but also going over complicated tasks like bypassing security features and fuzzing for new bugs.
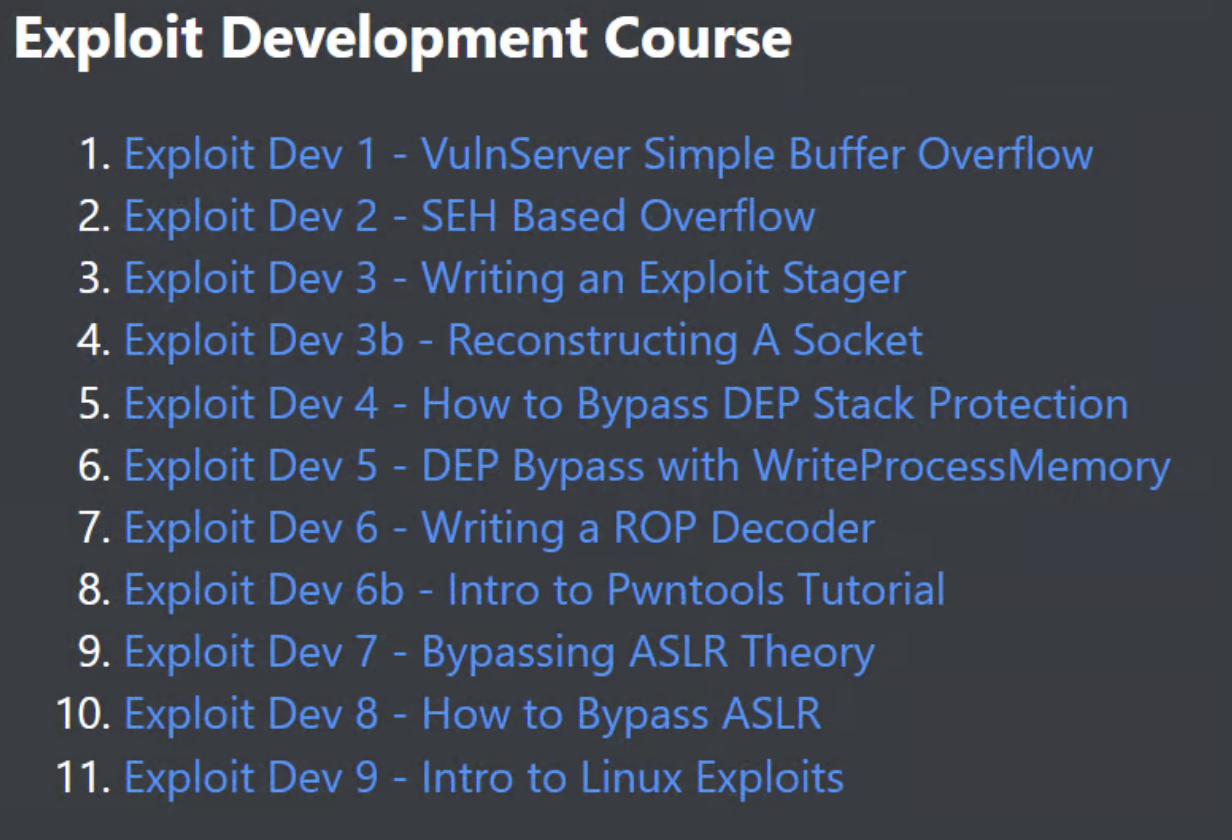
Linux Buffer Overflow – Exploit Development 9
(a teaser of chapter 9 of the course)
Starting with a Simple Buffer Overflow
The journey begins with an in-depth explanation of exploiting simple buffer overflows using VulnServer. This foundational chapter, available since September 3, 2022, guides students through reversing the VulnServer application using IDA Free, a popular disassembler. Participants will learn how to exploit a direct RET overwrite, a fundamental technique in binary exploitation. By the end of this chapter, you will be equipped to overwrite the return address during runtime, redirecting execution flow to their custom shellcode. This becomes the foundation of the course, with each chapter building upon this basic technique & adapting it to various increasingly difficult situations.
Course Overview
Guided Hacking’s Exploit Development Course is meticulously structured to provide a step-by-step learning experience. Each module builds upon the previous one, ensuring you don’t get lost or confused. The course includes lessons on buffer overflows, bypassing memory security features like Data Execution Prevention & deploying malicious shellcodes. Students will learn about a variety of different buffer overflow exploits including SEH-based overflows, which use the Windows Structured Exception Handler to gain reliable control over execution. The course also covers writing an exploit stager, handling large shellcodes with Winsock-based exploit stagers, and techniques for reusing existing sockets to bypass space restrictions.
Advanced Techniques and Topics
As part of the curriculum, learners will explore how to bypass DEP stack protection using Return Oriented Programming to bypass Data Execution Prevention, employing VirtualAlloc & WriteProcessMemory for DEP bypass. Advanced exploit techniques include:
-
Writing ROP decoders & leveraging pwntools for efficient exploit development
-
Overcoming Address Space Layout Randomization with partial RET overwrites
-
Transitioning from Windows to Linux exploitation by setting up a Linux VM and using gdb for debugging
(while this screenshot might look confusing now, after following the course you’ll have no problem jumping into assembly code like this)
Specialized Modules
The course also introduces students to egg hunter shellcode, while the term “egg hunter” might sound funny, this little trick to locate shellcode in memory will help you handle inaccessible memory regions to ensure reliable exploitation. Participants will learn to exploit use-after-free vulnerabilities to control the instruction pointer by understanding heap memory management and leveraging freed memory for arbitrary code execution.
(authors creative rendition of a “egg hunter”)
Expert Instructor
The course is led by a seasoned red team operator whose hacker handle is Nop, he has extensive experience in information security & exploit development. Having begun his infosec journey through university programs and certifications such as OSCP and OSED, the instructor now specializes in reverse engineering and binary exploitation.
He actually started as a student of Guided Hacking in 2020 and later applied for a job posting to make educational content for GH, this is a real success story showcasing the value of GH. His detailed and engaging tutorials show his passion for teaching and research. He regularly shares his knowledge at universities and conferences, making him a well known figure in the cybersecurity community.
(legendary author of Guided Hacking’s Exploit Dev Course)
Interactive Learning Experience
Guided Hacking’s Binary Exploit Development Course offers a unique blend of video tutorials & written articles. Each module is designed to be both informative and practical, encouraging hands-on learning. Students are urged to watch the accompanying video tutorials and refer to the written content as needed, ensuring a well-rounded understanding of each topic. Enroll Today
Students can enroll on the Guided Hacking website to gain full access to the Binary Exploit Development Course. By becoming a member, learners can view all course content, download exclusive software, receive updates on new modules and tutorials. A Guided Hacking subscription also includes 10 other courses and 1,300 text tutorials, so if you ever get lost, there is always another resource on the site to set you back on the path.
About Guided Hacking
Guided Hacking is a leading cybersecurity education platform dedicated to providing high quality, in depth training for beginners and professionals alike. With a focus on practical skills and real world applications, Guided Hacking’s courses cover various subtopics in the reverse engineering niche, including exploit development, malware analysis and game hacking. It’s truly a remarkable resource, there are so many tutorials that the owner of Guided Hacking says the hardest part of his job is keeping it all organized. If you want to checkout some of their free content to see what you might be missing out on, they regularly publish content on their YouTube channel.
The Post Guided Hacking Launches Comprehensive Binary Exploit Development Course first appeared on ZEX PR Wire
Information contained on this page is provided by an independent third-party content provider. Binary News Network and this Site make no warranties or representations in connection therewith. If you are affiliated with this page and would like it removed please contact [email protected]